Mach-O, APK and LLM Code Summary
Over the past few weeks, we have shipped three significant platform updates.
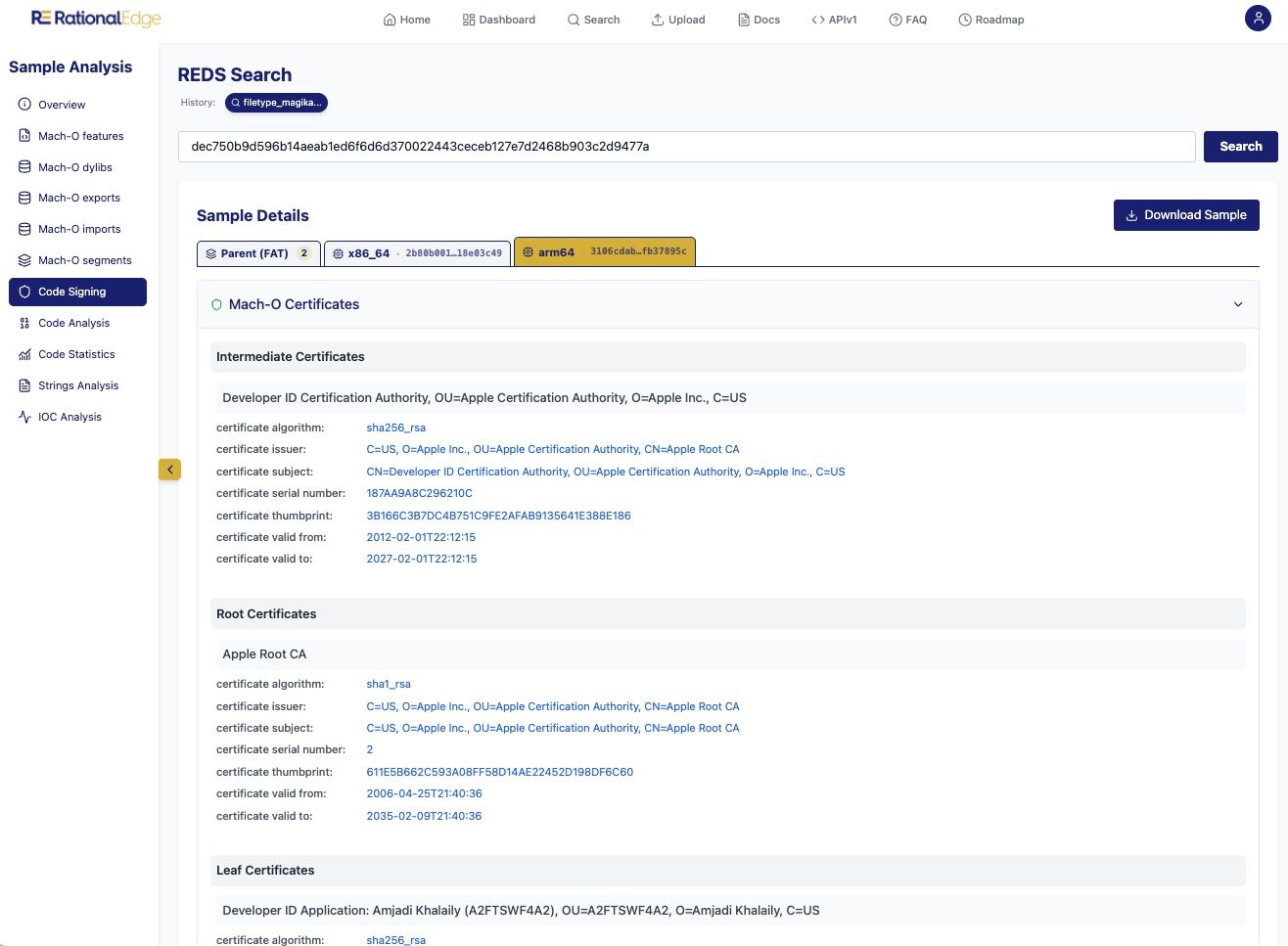
Mach-O Support
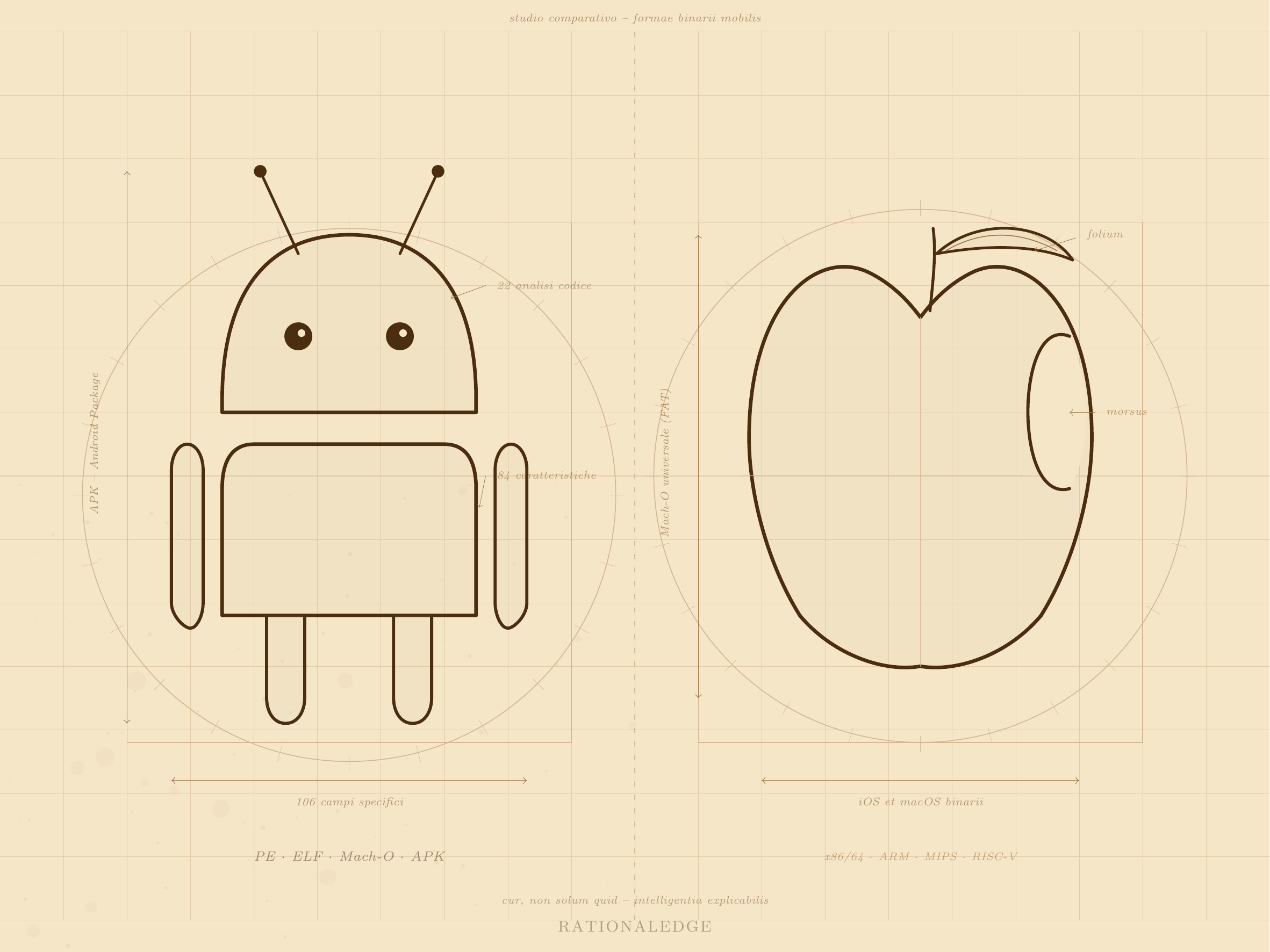
REDS now fully analyzes Mach-O binaries — both iOS and macOS — including Universal (FAT) formats. This is one of the most comprehensive Mach-O analyses you will find in any malware database and analysis platform. The capability is powered by machofile, our self-contained, open-source Python module built with a specific focus on malware analysis and reverse engineering, with zero external dependencies.
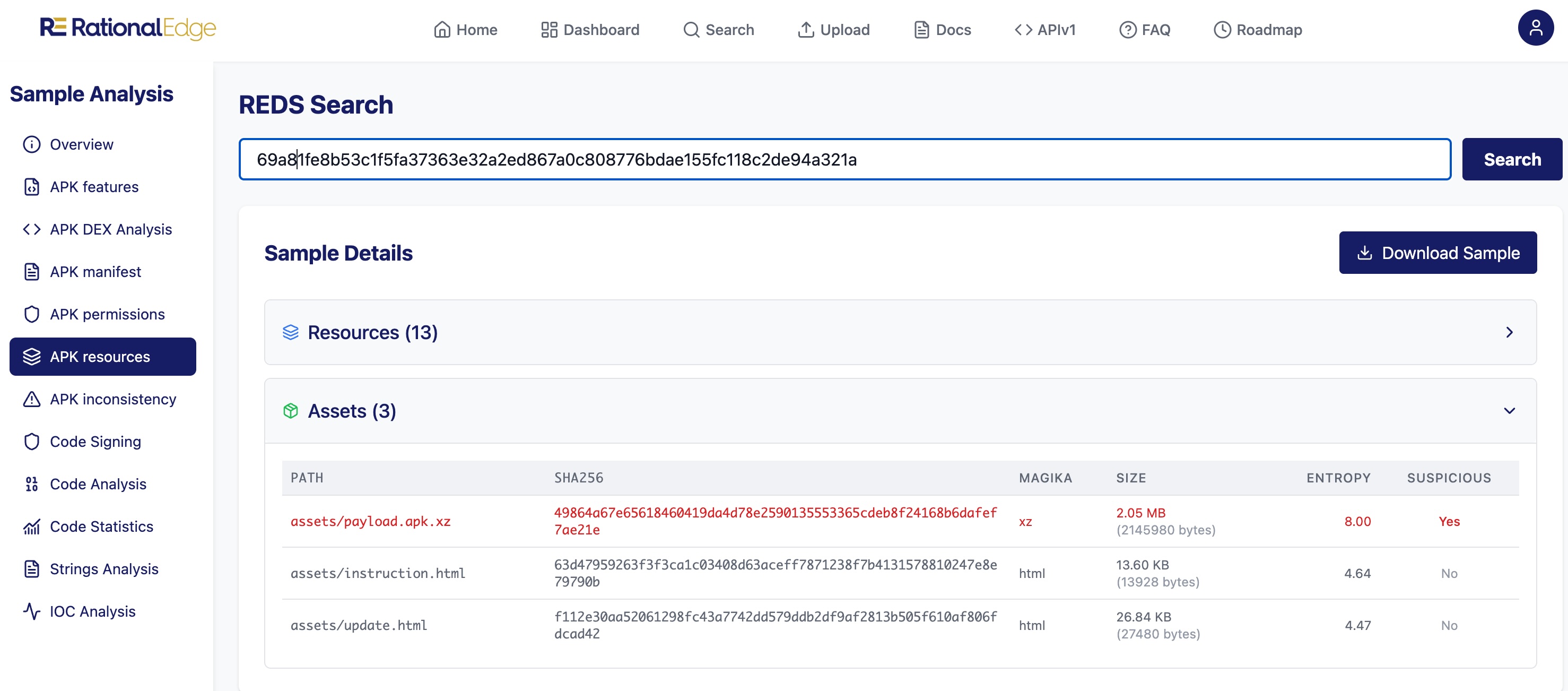
APK Support
Android application packages are now in scope, with 106 unique APK-specific fields available for search and correlation — 84 feature fields and 22 code analysis fields — on top of standard file attributes and metadata.
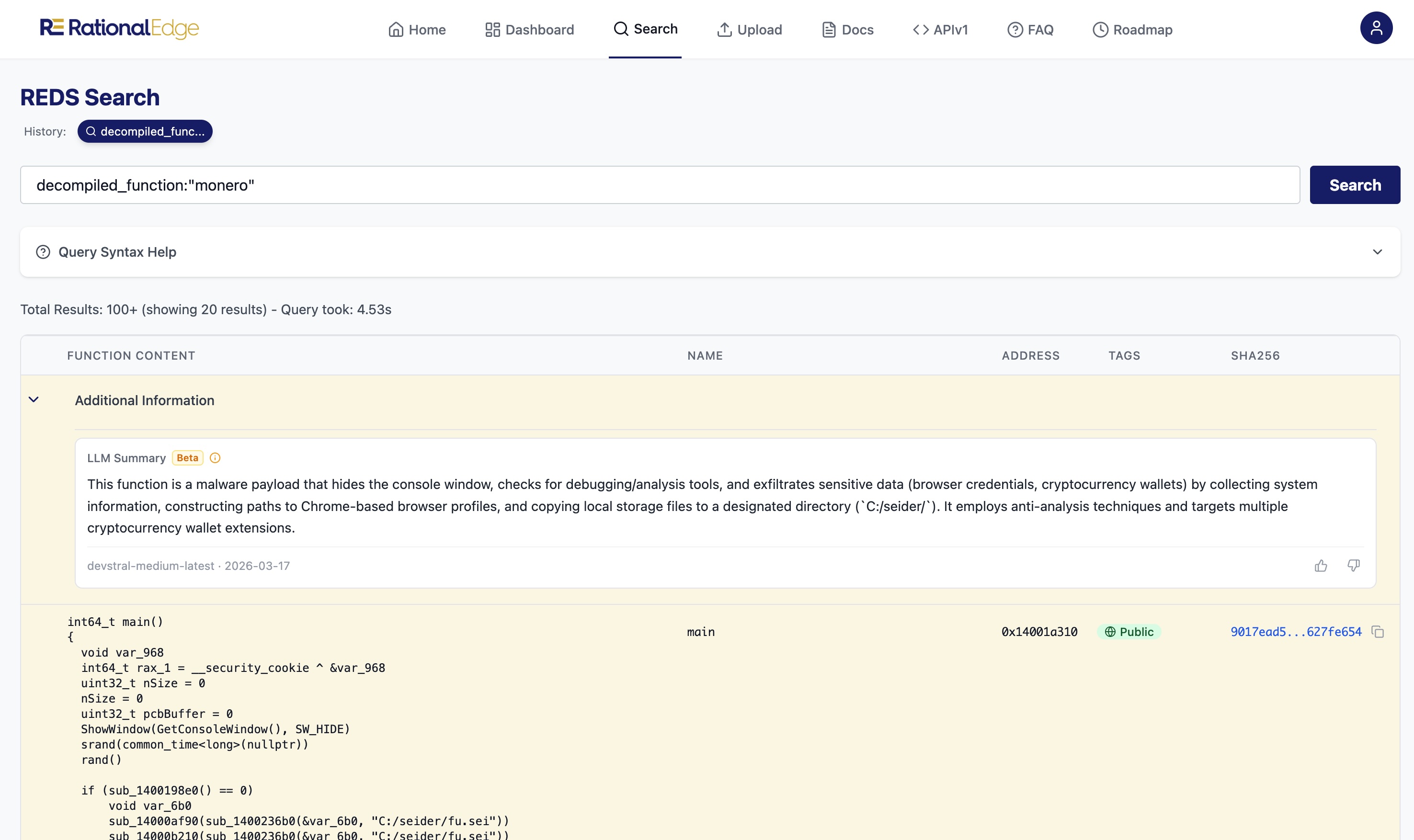
LLM-Assisted Code Analysis
Analysts can now ask questions about decompiled and disassembled functions directly from the analysis view. What does this function do? Why is this behavior suspicious? Instead of staring at code and piecing it together manually, you get context on function behavior and intent — another step toward the explainability we are building into everything. The goal has always been the same: show the evidence behind every assessment, not just a verdict.
With these releases, REDS now covers all four major OS platforms and file formats — PE, Mach-O (iOS and macOS), ELF, and APK — along with broad architecture support: x86/64, ARM/AArch64, MIPS, PowerPC, RISC-V (32/64-bit), and more. This brings full analysis coverage to samples targeting embedded and OT devices as well.
MoRE to come. Book a demo if you want to see it in action.